Google also issued a warning: there is a risk to the $100 billion worth of assets in Ethereum, and five major quantum attack vectors have been exposed.
A Google white paper reveals that quantum computers could deal a severe blow to Ethereum, with whale wallets, DeFi key management, and staking systems facing risks in the hundreds of billions of dollars.
In a report released Monday by Google’s Quantum AI team, nearly all the attention of the crypto community is focused on Bitcoin: a 9-minute break, up to a 41% chance of theft, and 6.9 million BTC exposed to risk—but the report’s coverage of “Ether” has received little market attention. Little do people know that the risks hidden in it are even more shocking, and investors as a whole should treat them with the highest level of alert.
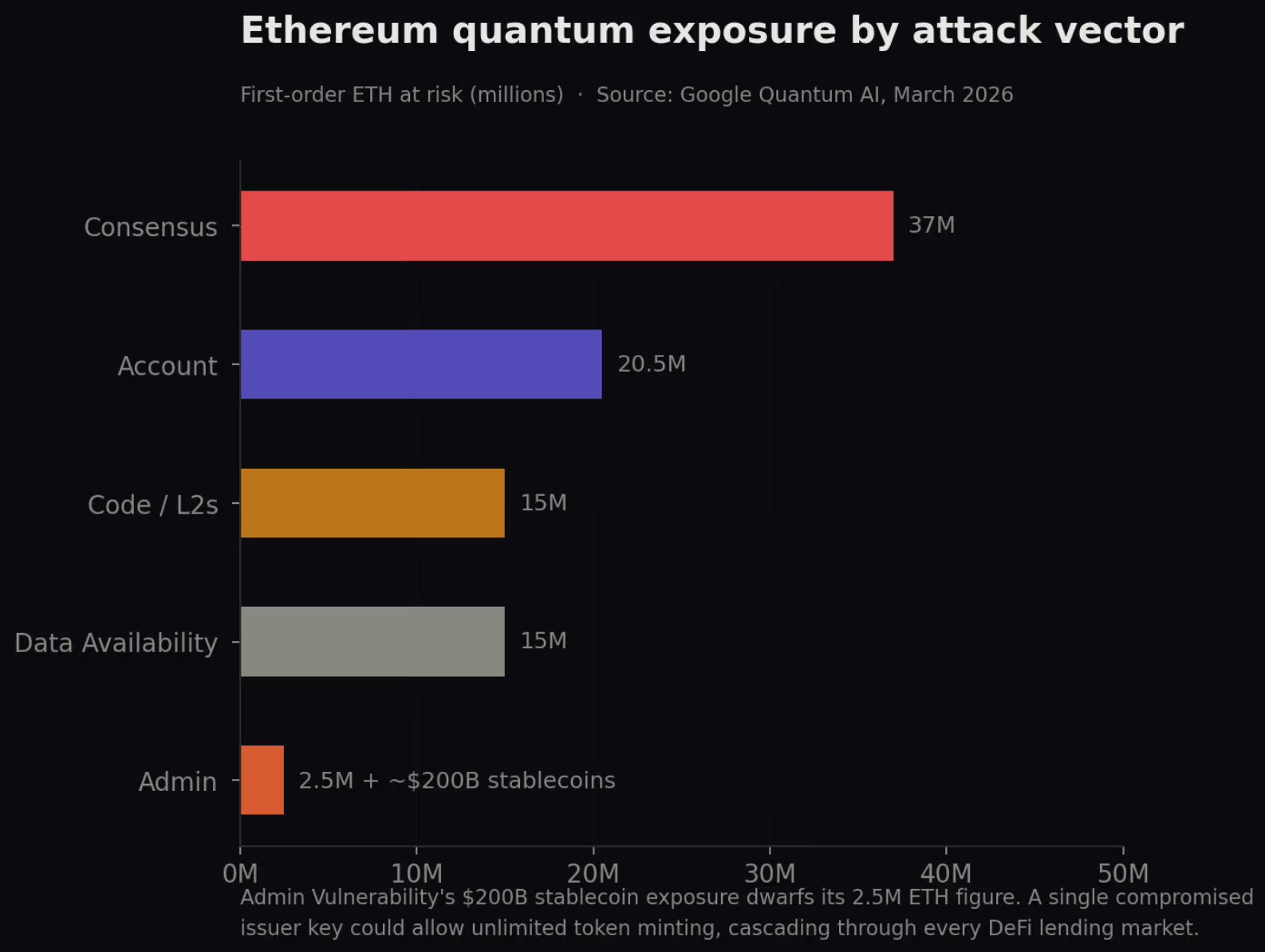
Written jointly by Google, Justin Drake—an Ethereum Foundation core researcher—and Dan Boneh, a cryptography luminary at Stanford University, the white paper analyzes the “five most fatal paths” through which future quantum computers may break Ethereum. Each path could precisely strike different lifelines of Ether, and based on current token prices, the value of assets directly exposed to risk has already surpassed $100 billion. If it triggers a domino effect, the damage will be impossible to estimate.
Image source: Google
- “Barefaced” whale wallets
In the world of Bitcoin, users’ “public keys” can be hidden behind a hash function (Hash, a kind of digital fingerprint) before they are actually spent. But on Ethereum, as soon as a user sends a transaction, the public key becomes “permanently publicly visible” on the blockchain. Unless you completely abandon that account and move the funds away, you basically can’t change it.
Google’s team estimates that currently the top 1,000 whale wallets by ETH balance (total holdings of about 20.5 million Ether) are already fully exposed to risk. If a quantum computer can break a single set of private keys in just 9 minutes, in under 9 days, those 1,000 whale wallets would be looted clean.
- The “super admin” that keeps DeFi’s life and death ledger
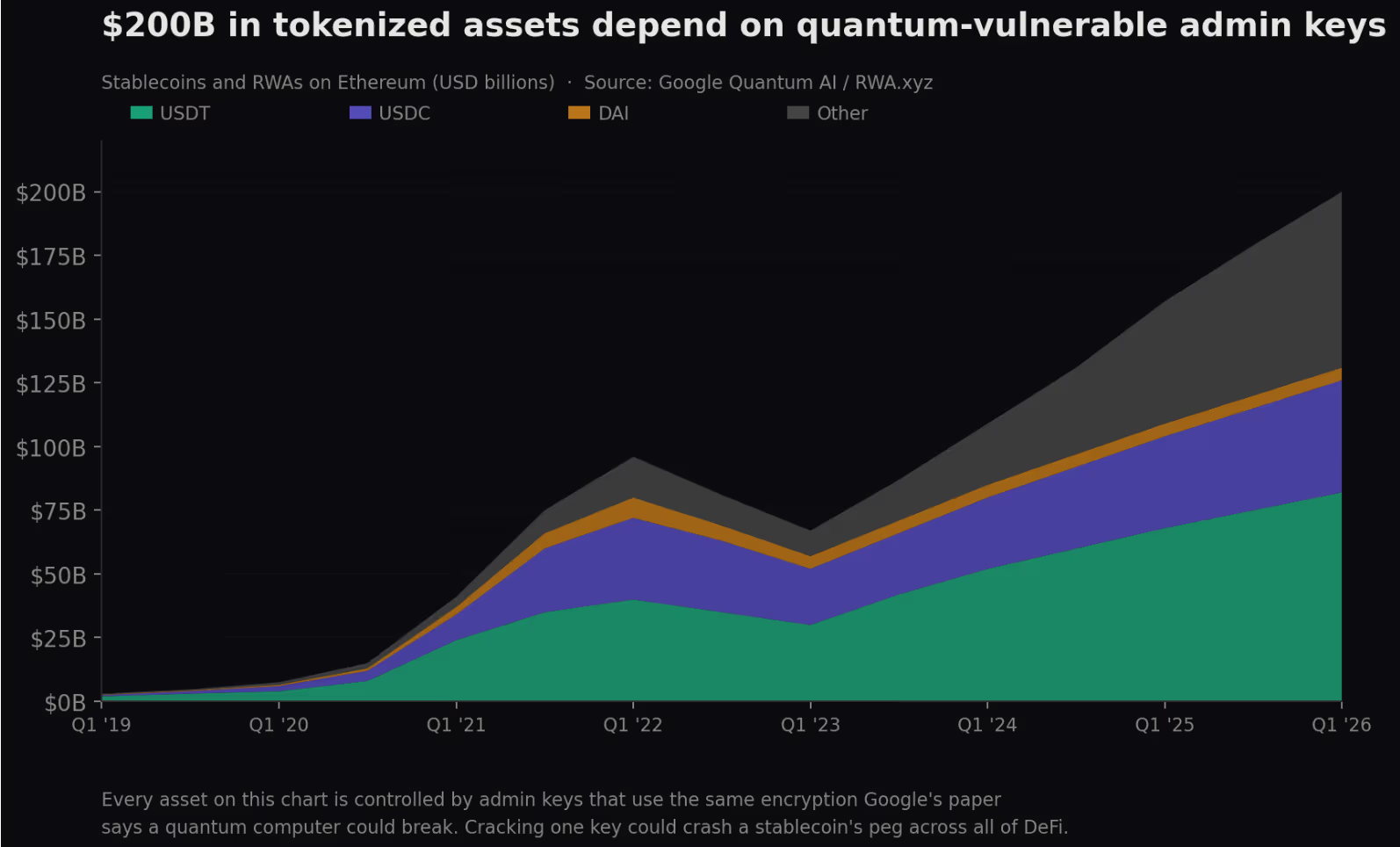
Smart contracts on Ethereum that support lending, trading, and stablecoin issuance typically grant “special privileges” to a small number of administrators, allowing a “super admin” to pause contracts, upgrade code, or even transfer massive sums of funds. The report finds that at least 70 large contract administrators’ key(s) have been exposed on-chain, involving about 2.5 million Ether.
More hair-raising are the ripple effects beyond Ether. These administrator accounts also hold the “minting rights” for mainstream stablecoins such as USDT and USDC. In other words, once a quantum hacker breaks one of these keys, it could mint tokens endlessly—like an automated printing press—creating ripple effects across lending markets that use these tokens as collateral.
The white paper estimates that on Ethereum, stablecoins and tokenized assets worth as much as $200 billion rely on these fragile administrator keys.
Image source: Google
- Layer2 that depends on the same set of cryptography
To increase transaction speed, most Ethereum transactions are processed off-chain through Layer 2 solutions such as Arbitrum and Optimism, then the results are returned. But here’s the problem: the built-in encryption tools that these Layer2 rely on on Ethereum all lack the ability to resist quantum cracking.
Rough estimates in the report suggest that across major Layer2s and cross-chain bridges, at least 15 million Ether are exposed to risk. Currently, the only thing considered safe is StarkNet, which uses hash algorithms (rather than elliptic curve signature algorithms).
- Attack the “staking system” to bring the network to a standstill
Ethereum relies on a “Proof-of-Stake (PoS)” mechanism to maintain network security, where validators vote on which transactions are valid. However, the report believes that the digital signature verification mechanism used for these votes is also vulnerable to being cracked by quantum computers.
There are currently about 37 million Ether across the network in a staking state. If hackers successfully control one-third of the validating nodes, they can stall the network, causing transactions to be unable to be confirmed. If they control two-thirds of the validating nodes, hackers could even effectively take over the entire system and directly tamper with the blockchain’s historical records.
The report also specifically warns that if staking funds are overly concentrated in large pools (for example, Lido, which has an estimated market share of about 20%), hackers only need to focus their fire on a single provider’s infrastructure to significantly shorten the attack timeframe.
- A “permanent vulnerability” that only needs to be cracked once
The report also mentions a most special and most worrying attack path. Ethereum uses a system called “Data Availability Sampling” to verify whether the transaction data returned by Layer2 truly exists. During initial setup, this system generated a set of “absolute secret numbers” that should have been thoroughly destroyed afterward.
Once hackers activate quantum computers, they can reconstruct these secret numbers from publicly available data. Most terrifyingly, once cracked even once, these secret numbers become a set of tools that can operate permanently. Even if hackers do not use quantum computers, they could permanently forge data verification proofs.
Google’s team even describes that this vulnerability tool has “high transactional value.” Once it enters the black market, every Layer2 network that relies on Ethereum’s Blob data system will be affected.
A rescue battle for $100 billion: Ethereum’s defense war and weak spots
Of course, the Ethereum camp isn’t just sitting idle. Justin Drake, an Ethereum Foundation researcher and co-author of the white paper, reveals that the foundation officially launched a research gateway for the “post-quantum” era last week. It says the related research has been ongoing for more than 8 years, and that the testnets are currently being advanced every week, along with a multi-stage hard fork upgrade roadmap. The goal is to fully introduce quantum-resistant cryptography before 2029.
In addition, compared with Bitcoin, which produces a block every 10 minutes, Ethereum’s extremely fast block time of just 12 seconds also makes it much harder for hackers to execute real-time transaction interception.
However, the white paper also reminds: even if Ethereum mainnet successfully upgrades, the thousands of smart contracts already deployed on-chain will not automatically become immune.
This means every DeFi protocol, every cross-chain bridge, and every Layer2 network must upgrade their code and replace keys on their own. In the decentralized world, there is no central institution that can force everyone to press the upgrade button. For the crypto ecosystem, this survival battle racing against quantum technology has only just started the sprint.
- This article is republished with authorization from: 《Blocker (區塊客)》
- Original title: 《“Five major quantum attack paths” exposed! Google issues a warning: $10 billion in assets on Ethereum at risk》
- Original author: Block Sister MEL